Most secure web gateway vendors will tell you they support macOS. What they mean is that a Mac agent exists. What they do not mean is that the Mac agent ships the same features, on the same release date, with the same performance characteristics as the Windows agent.
In a mixed fleet, that gap is a compliance problem before it is a user-experience problem. A policy that blocks an upload on Windows but not on macOS is not one control with two implementations. It is two controls with different effectiveness, and the weaker one defines the risk.
A secure web gateway with true Mac and Windows parity ships identical features on the same release date, runs natively on Apple Silicon, and produces the same events on both platforms.
The Mac-as-Second-Class Tax
The pattern repeats across the industry. Vendors build for Windows first, port to macOS months later, and leave one or two features Windows-only forever. In interviews with security teams running mixed fleets, three gaps come up again and again.
The first is DLP coverage. Windows agents inspect clipboard, file uploads, and removable media. Mac agents often skip one or two of those surfaces. The second is SSL inspection performance. Without an Apple Silicon native build, the Mac agent runs under Rosetta, spikes CPU, and users disable it. The third is release cadence. A feature ships to Windows in one quarter and macOS in the next, which means for months the control is uneven.
If your fleet is 40 percent Mac, your control is 40 percent weaker than the marketing suggests. A parity checklist surfaces this before you sign.
Parity Checklist: Ten Items to Verify
Run through this list with the vendor SE in the room. The correct answer to every item is “identical on both platforms, shipping today.”
1. SSL Inspection
Same inspection engine, same certificate handling, same bypass list format. No hidden category differences.
2. DLP Surfaces Covered
Web uploads, clipboard, drag-and-drop, removable media. Each surface tested on both platforms with the same rule set.
3. Content Classification
The same classifier runs on both. An LLM-based secure web gateway should produce the same verdict on the same document regardless of OS.
4. Shadow AI Controls
The same category of consumer GenAI services blocked on both. Not “Windows blocks these 50, Mac blocks these 30.”
5. Policy Engine Feature Support
Every policy primitive you use on Windows supported on Mac. User, group, time window, destination, category, content class.
6. Logging Schema
Event fields identical across platforms. Analysts should not need to learn two event formats.
7. Tamper Protection
End users cannot disable the agent without admin credentials, on either platform. Mac-specific quirks like full disk access and system extension approval handled by the installer.
8. Native Architecture
Apple Silicon native binary. No Rosetta translation. Windows ARM support if the fleet includes ARM laptops.
9. Release Cadence
Features ship on the same release date. Ask to see the last four release notes from both platforms side by side.
10. MDM Deployment
Jamf and Kandji support for Mac, Intune for Windows, consistent profile structure across both.
If the Mac answer is a roadmap date, the parity is a roadmap promise.
Apple Silicon Native vs Translated
Apple Silicon is now the default in engineering and design teams. A translated agent pays a measurable cost. Rosetta translation adds latency to every system call the agent makes, and an agent that inspects every network request makes many. Battery life drops, fan noise increases, and the SSL inspection throughput on large downloads falls behind a native build by a meaningful margin.
The test is simple. Ask the vendor whether the shipped binary is arm64 native or x86_64 under Rosetta. The file command on the installed binary gives a straight answer. A native build also matters for HTTP/2 performance, because any downgrade the agent introduces is magnified when the base path is already slower than it should be.
How to Test Parity in a POC
The POC is where vendor marketing meets fleet reality. Use a parallel test matrix.
| Test | Windows result | macOS result |
|---|---|---|
| Block upload of unstructured PII document | ||
| Block paste of source code into consumer GenAI | ||
| Inspect SSL traffic to new.example domain | ||
| Enforce time-window policy on social categories | ||
| Produce event with user, destination, reason fields | ||
| Inspection under 10 ms added latency p95 | ||
| RAM footprint under 100 MB steady state | ||
| Native binary for the platform CPU | ||
| Jamf or Kandji vs Intune deployment parity | ||
| Tamper protection holds against local admin attempt |
Run each test the same day on both platforms. Fill the matrix in the console side by side. A real parity product fills the grid cleanly. A parity-in-marketing product has caveats in half the cells.
A swg that passes this matrix once will pass it every release, because parity is a property of the architecture, not of each release cycle.
Policy Drift Between Platforms
Uneven features produce uneven policies. Over time, administrators adapt policy to the weaker platform, because consistent enforcement across a mixed fleet matters more than peak capability on one side. The way to catch it is to require the policy export to be identical across platforms. If the export differs, the product is not truly unified and the drift will come back in an audit finding.
Parity as a First-Class Requirement
For any mixed fleet, Mac and Windows parity is not a nice-to-have. Put it in the RFP, test it in the POC, and walk away from any vendor that treats Mac as a second release train. Teams that enforce this early avoid the audit finding that traces uneven coverage to a Mac-Windows gap.
FAQ
What is a secure web gateway?
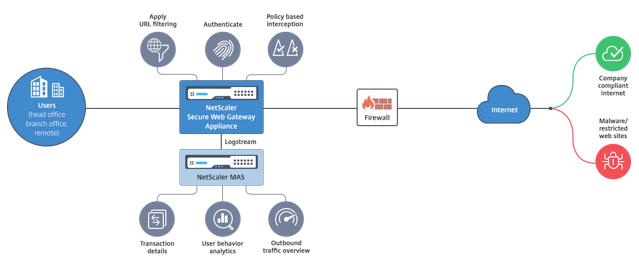
A secure web gateway inspects outbound web traffic from user devices and enforces policy on destinations, categories, and content. In a cross-platform context, the SWG matters only to the extent it behaves the same way on every device in the fleet.
How to enable secure web gateway on macOS?
Deploy the agent via an MDM tool such as Jamf, Kandji, or Mosyle. The profile should grant full disk access, approve the system extension, and scope the agent to the target user group. A well-designed agent requires no manual approval from the end user beyond the MDM prompt.
What about Microsoft-specific SWG features?
Windows-only features such as deep Defender integration or Entra conditional access tie-ins are legitimate Windows strengths, but they should not come at the cost of macOS gaps. A unified product exposes Microsoft integrations on Windows while maintaining parity on everything else for Mac users. Ask the vendor to separate platform-specific integrations from core inspection and DLP parity.
Is Apple Silicon native support really necessary?
Yes. A translated agent burns battery, heats the laptop, and slows SSL inspection. Mac-first vendors like dope.security have shipped Apple Silicon native for years, so a translated agent in 2026 indicates the vendor has not kept up. Native support is table stakes.